Manufacturing News
Federal government needs to set an example on cybersecurity
Government Accountability Office says federal agencies need to do their own homework before they can help the private sector

Photo courtesy of Getty Images/Nico El Nino
While food and beverage processors have been scrambling to protect their process control equipment, intellectual property (IP) and IT/OT systems from cybersecurity/ransomware attacks, their efforts may be outpacing the Federal Government, which should be setting an example by having secured its own agencies from cyberattacks. How can the federal government provide cybersecurity assistance to private and public companies when its own cybersecurity affairs may not be in order?
In a recent Government Accountability Office (GAO) report entitled, “Cybersecurity: Federal Actions Urgently Needed to Better Protect the Nation’s Critical Infrastructure,” GAO found that out of 3,700 recommendations made to government agencies directed at fixing cybersecurity shortcomings, as of November 2021, 900 of those recommendations were not yet implemented.
In July 2019, GAO reported on key practices for establishing within 23 government agencies, an agency-wide cybersecurity risk management program that includes designating a cybersecurity risk executive, developing a risk management strategy and policies to facilitate risk-based decisions, assessing cyber risks to the agency, and establishing coordination with the agency’s enterprise risk management program.
GAO reports that the 23 federal agencies created a risk executive, but they often didn’t incorporate other key practices in their programs—such as establishing a cybersecurity risk management strategy or a process for assessing agency-wide cybersecurity risks or establishing a process for coordinating between cybersecurity and enterprise risk management programs for managing all major risks. In fact, GAO made 57 recommendations to these 23 government agencies in 2019, and as of November 2021, 25 of these recommendations have yet to be implemented.
Protecting private and public infrastructure and systems
To address critical private and public infrastructure cybersecurity issues, GAO recommended that the federal government should develop and execute a comprehensive national cyber strategy and strengthen the federal role in protecting the cybersecurity of critical infrastructure.
In 2020 research, GAO found it wasn’t clear in 2018 who was responsible for establishing national cyber strategies and asked Congress to consider legislation to designate a position in the White House to lead the effort. In January 2021, a federal statue established the Office of the National Cyber Director within the Executive Office of the President.
In October 2021, the national cyber director issued a strategic intent statement, outlining a vision for the director’s planned high-level lines of efforts. The establishment of a national cyber director is an important step toward positioning the federal government to better direct activities to address the nation’s cyber threats. Nevertheless, GAO’s recommendation to develop and execute a comprehensive national cyber strategy is not yet fully implemented. As a result, a pressing need remains to provide a clear roadmap for addressing the cyber challenges facing the nation, including its critical infrastructure.
February 2013: White House issued Executive Order 13636, “Improving Critical Infrastructure Cybersecurity.”
February 2013: Presidential Policy Directive 21, “Critical Infrastructure and Resilience.”
February 2013: Executive Order 13636 declared NIST to lead the development of a flexible performance-based cybersecurity framework.
February 2014: NIST publishes its first framework of cybersecurity standards and procedures. It is updated to version 1.1 in 2017.
November 2018: Cybersecurity and Infrastructure Security Agency (CISA) Act of 2018 established CISA within DHS to advance the mission of protecting federal/civilian agencies’ networks from cyber threats and to enhance the security of the nation’s critical infrastructure.
2021: National Defense Authorization Act (NDAA) established roles and responsibilities for lead agencies, known as sector risk management agencies, in protecting the 16 critical infrastructure agencies.
In terms of the federal role in protecting the cybersecurity of critical infrastructure, CISA (Cybersecurity and Infrastructure Security Agency) within the Department of Homeland Security (DHS) was charged with responsibility for, among other things, enhancing the security of the nation’s critical infrastructure in the face of both physical and cyber threats.
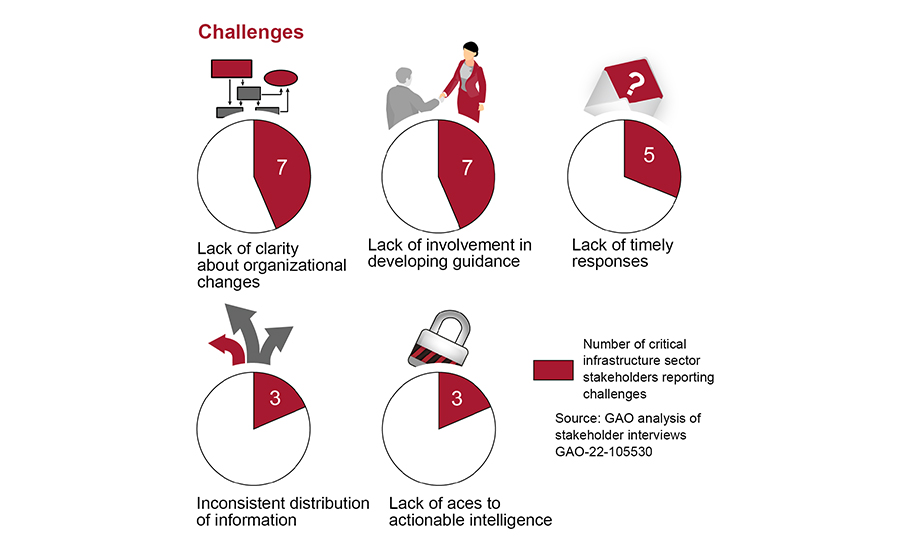
In March 2021, GAO reported that DHS needed to complete key activities related to the transformation of CISA, including finalizing the agency’s mission-essential functions and completing workforce planning activities. GAO also reported that DHS needed to address challenges identified by selected critical infrastructure stakeholders, including having consistent stakeholder involvement in the development of related guidance. Accordingly, GAO made 11 recommendations to DHS. As of November 2021, DHS had not yet implemented them, though it stated its intent to do so.
Federal government’s role in cybersecurity
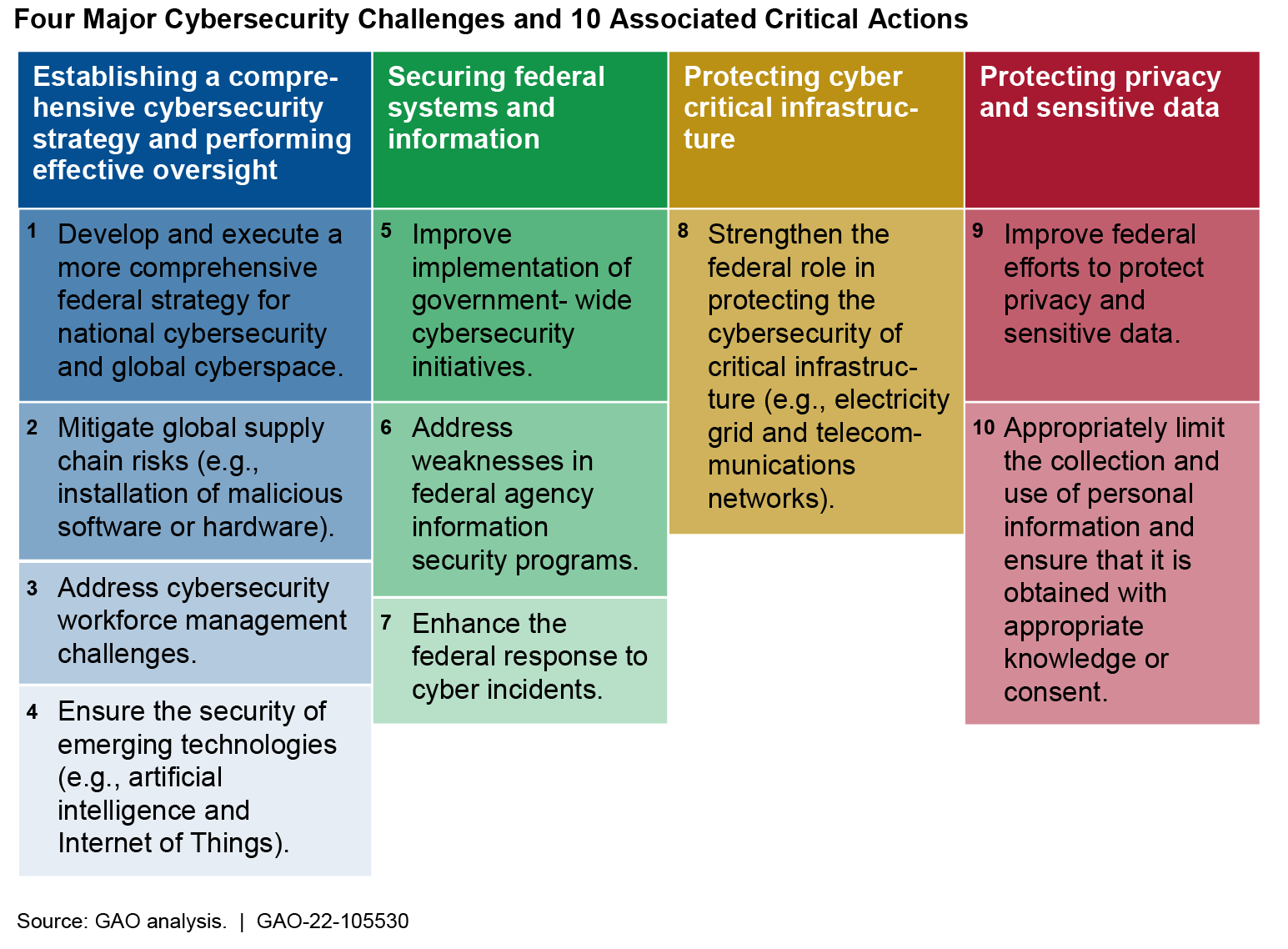
The GAO classified four key cybersecurity challenges facing the nation’s private sector and recommended several associated critical federal actions to address these challenges.
1. Establish a comprehensive cybersecurity challenge: Develop and execute a more comprehensive federal strategy for dealing with cybersecurity issues. Mitigate global supply chain risks (e.g., installation of malicious software or hardware). Address cybersecurity workforce management challenges. Ensure the security of emerging technologies (e.g., AI, IoT).
2. Secure federal systems/information: Improve implementation of government-wide cybersecurity initiatives. Address weaknesses in federal agency information security programs. Enhance the federal response to cyber incidents.
3. Protect cyber-critical infrastructure: Strengthen the federal role in protecting the cybersecurity of critical infrastructure (e.g., electric grid, communications systems).
4. Protect privacy and sensitive data: Improve federal efforts to protect privacy and sensitive data. Limit the collection and use of personal information and ensure that it is obtained with appropriate knowledge or consent.
Among 16 private and public critical infrastructure sectors, GAO says CISA still needs to do a lot of work in addressing: a lack of clarity about organizational changes, lack of involvement in developing guidance, lack of timely responses, inconsistent distribution of information and a lack of access to actionable intelligence.
For more information on this study, visit https://www.gao.gov/products/gao-22-105530
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





