Manufacturing News
How food processors can protect against cybersecurity breaches
Unreported attacks may hide the extent of the challenge
According to Verizon’s 2017 Data Breach Investigations Report, 75 percent of actual breaches were caused by outsiders, and 25 percent involved internal actors, while 18 percent were conducted by state-affiliated parties, and more than half involved organized criminal groups. As many as 62 percent of breaches were caused by hacking, 51 percent included malware, 81 percent leveraged stolen and/or weak passwords, and 43 percent were social attacks.
Verizon’s statistics are based on actual events—not polls. Industrial control systems are not exempt from attacks, but with the knowledge of how attacks occur, with new tools coming onto the scene and with long-term investments in cybersecurity, processors stand a better chance of keeping their plants safely up and running.
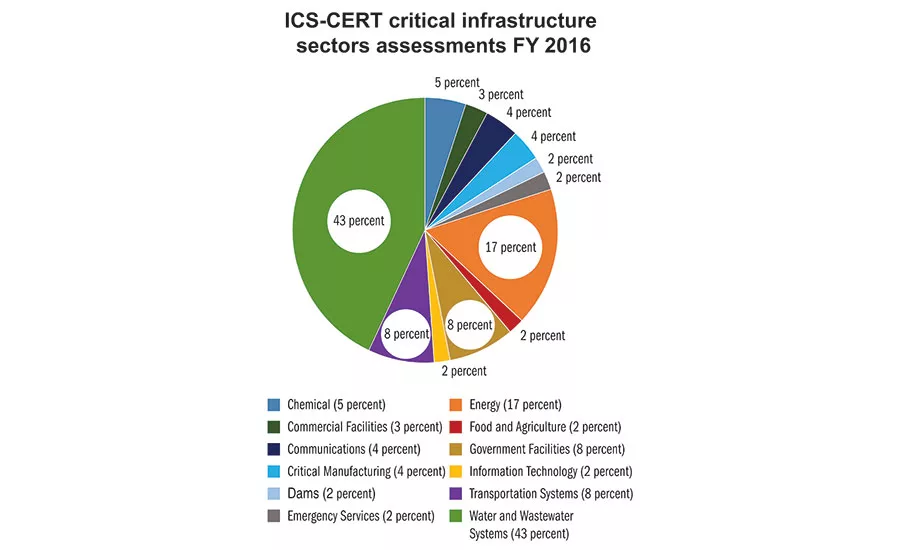
ICS-CERT (Industrial Control Systems-Cyber Emergency Response Team) recently released its Annual Assessment Report for Fiscal 2016. The report highlights continued and significant risks to industrial control systems. ICS-CERT also released Version 8.0 of its Cybersecurity Evaluation Tool (CSET). The team identified 700 incidents for the year through design architecture reviews, as well as network validation and verification assessments.
For the third year running, boundary protection was the most commonly identified area of weakness, and weaknesses related to boundary protection accounted for 13.4 percent of all discovered weaknesses. The next three weakness categories, in order of prevalence, were least functionality, identification and authentication, and physical access control.
In boundary protection, the two major risks reported were undetected unauthorized activity in critical systems and weak boundaries between ICS and enterprise networks. Least functionality risks include increased vectors for malicious third-party access to critical systems and rogue internal access.
Identification and authentication risks include a lack of accountability for user actions on compromised accounts and increased difficulty in securing accounts when personnel leave a company. Physical access control risks include unauthorized physical access to field equipment and locations where someone could access the ICS network, steal or vandalize cyber assets, add rogue devices or make changes to programs or device firmware.
The latter issue (changes to programs or firmware), however, is not limited to physical tampering alone. A new vector was discovered with the 2014 Dragonfly/Havex attack, otherwise known as a remote access Trojan (RAT), which was embedded into firmware updates on various automation vendors’ websites. The virus payload would cause multiple common OPC platforms to crash, which could cause a denial of service effect on applications reliant on OPC communications.
“We all know that ICS and IIoT asset owners depend on their vendors to supply valid software and firmware for system implementation and upgrades,” says Eric Byres, PE, ISA Fellow, noted industrial security expert and inventor.
Byres’ firm, aDolus, is now working on a US Department of Homeland Security-funded research project to investigate the viability of using trust anchor technologies for real-time verification of ICS software/firmware packages.
The industry needs a robust and universal solution for safeguarding against the counterfeiting of firmware/software upgrades.
“Our project is investigating methods of generating digital fingerprints of both legitimate and suspect firmware via automated agents and then assigning reputational scores to the software package,” says Byres. “An API and web tool we’re developing allows end users to incorporate a validation process into their daily operations, ensuring the legitimacy of updated firmware/software without impeding critical operations.”
In other words, a technician at a site uses the tool to scan any firmware upgrade package just before loading it into a controller, says Byres. The tool then gives the software/firmware a score between one and 10, where 10 means the software bundle is highly validated and thus safe, while one means it is pure evil malware.
Part of the problem is that plant managers find it difficult to convince their CEOs to fund ongoing cybersecurity investments. These investments are often defined as short-term projects and are not positioned as long-term investments for conducting business.
Plant managers need to link their cybersecurity proposal to business benefits. For example, it’s not unreasonable to think that a cyberattack could put your business on hold for a few days or a week while you rebuild the system(s) from backups.
For more information:
Eric Byres, aDolus Inc., eric.byres@aDolus.com, 866-897-9980.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!




