Tech Update
PLCs and controllers are being used as intelligent gateways to IIoT
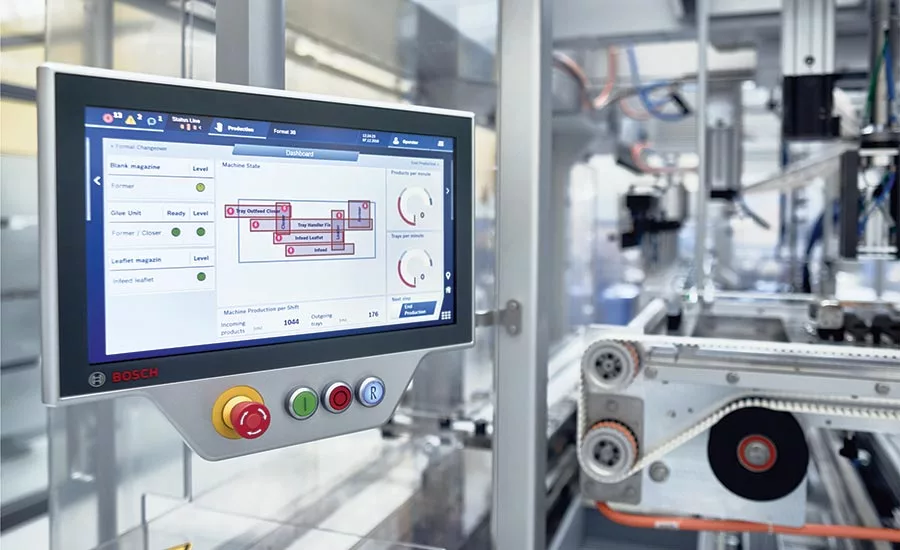
Bosch Packaging implements Beckhoff IP 65-rated CP3716 Panel PCs, which combine a 15.6-inch, multitouch HMI and powerful PC-based controller with up to quad-core Intel Atom processors.
Photo courtesy of Beckhoff

Schneider Electric’s Modicon M262 IIoT-ready controller has direct connectivity to the cloud with cybersecurity and handles four to 16 synchronized axes with scalable cycle time down to 1.0 ms and a 3.0 ns processing speed independent from communication tasks.
Photo courtesy of Schneider Electric

AutomationDirect offers many affordable PLC options, including its Do-more, Productivity and CLICK PLC families.
Photo courtesy of AutomationDirect

Bosch Rexroth intelligent motion controllers integrate motion with robotics to provide synchronized product and carton tracking, increasing efficiency.
Photo courtesy of Bosch Rexroth Intelligent Motion Controls
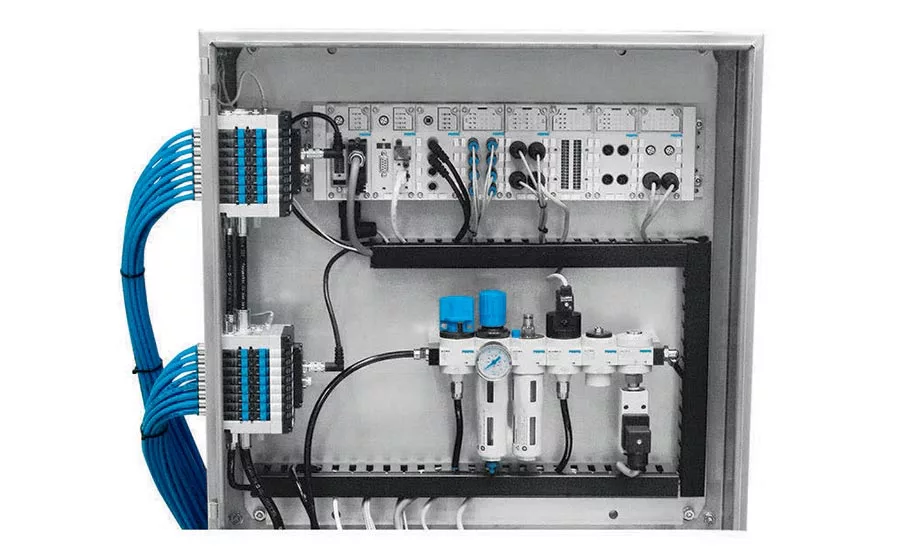
Festo’s CPX Terminal (top section) provides an integrated platform for remotely controlling valves.
Photo courtesy of Festo
It isn’t that the terms programmable logic controller (PLC) and programmable automation controller (PAC) are necessarily divorced from IIoT; in fact they may form the very core of IIoT.
But early on, I want to get the term “IIoT” out of this discussion on PLCs/PACs and focus on what they do best: receive data from sensors, intelligently control a process (e.g., discrete, batch or continuous, motion control, robotics), orchestrate a group of subordinate controllers, and provide data about what they’re doing to other key information subscribers in the enterprise. We’ll cover more on the IIoT aspect in an online story—so stay tuned!
As one interviewee suggested, the term “PLC/PAC” may still conjure up a vision of a very basic device for handling I/O processes, but it’s not necessarily the case for today’s more technically advanced PLCs. Current state-of-the-art PLCs/PACs may have extremely powerful communications onboard, “cloud” connectivity and even digital simulation capabilities to make them critical components in control ecosystems. Years ago, they probably operated on a proprietary industrial network (remember token-passing architectures?) or 10 Mbit Ethernet, but now most operate on open 1 Gbit—or faster—Ethernet, though they may still use proprietary application protocols.
PLCs/PACs are the unseen workhorses in our processes and material handling/packaging equipment today. Yet they’re ubiquitous with prices on some models starting under $100, and many use either open-source or proprietary operating systems (OSs). Today’s controllers often are capable of withstanding not only harsh physical environments, but also dumb programming mistakes made by harried technicians and engineers, and would-be hack attacks emanating from outside or inside the industrial network.
Jacks of all trades
Modularity has always been a hallmark of many PLCs, allowing an engineer to add capabilities as needed, with plug-in processors, I/O boards and expansion modules. For example, Mitsubishi’s newest iQ-F series of compact controllers is built on the company’s FX family and can be used for simple control of discrete I/O, but is also capable of PID (analog loop control), networking and synchronized multiaxis motion control. The model iQ-R modular controller expands capabilities to include safety, integrated robotics and connectivity to MES/ERP—all from the same platform, says Lee Cheung, product engineer. Solutions scale seamlessly as both models can be programmed with the same software, which can combine ladder, function block diagram or structured text languages.
Yet there is still a need for simplicity, and there are low-cost options to fill the bill for small applications with simple control. Bill Dehner, technical marketer at AutomationDirect, suggests an engineer can opt for the CLICK PC line of PLCs, which start at $69 and feature easy-to-use, free programming software. For more involved applications, engineers can select the BRX PLC series, which has advanced instruction sets and features coordinated motion control, HTTP communications and integrated security. Beyond that level, the Productivity line is a scalable offering with three distinct hardware platforms, all using free software. While ladder logic tends to be the primary programming language, Dehner notes that many C++ type languages are finding their way into industrial controls, bringing along many open-source options.
Beckhoff provides a vast range of scalable industrial PC (IPC) options with prices that have remained steady—and even declined in many cases—over the years, says Eric Reiner, industrial PC product manager, USA. These include ultra-compact embedded controllers suitable for basic PLC functions up to multicore industrial servers to enable intelligent motion control and robotics, machine vision, machine learning and other advanced tasks on the same controller. Beckhoff also offers IP 65-rated panel PCs, which integrate multitouch HMI in numerous sizes and powerful PC-based controllers. As a result, engineers can select the right controller for each application, even in environments that have high temperatures, dust or combustible atmospheres.
Compare and contrast
Is there any one yardstick to compare PLCs today? Can you compare PLCs on I/O count or cost per I/O?
“Because Bosch Rexroth controllers grew out of motion control, we tend to measure our controllers by the number of drives the controller can handle,” says Allen Tubbs, product manager, Bosch Rexroth. Even that is becoming difficult, as is measuring PLC/PACs by I/O count. The controllers are tasked with much more than I/O control, so it becomes difficult to pick a simple metric to do a side-by-side comparison of PLCs.
“It becomes increasingly necessary to compare processing power and memory, but even then you need to know a lot about how the PLC processes information, how often tasks will be running in the application, and what sort of data systems will be polling the control,” adds Tubbs. Because the feature list and capability of PLCs have grown over the years, it has become difficult to do a side-by-side comparison.
Until a project is completed, the number of I/O could be elusive. For example, one project that Concept Systems (a Control System Integrators Association member) recently finished had somewhere between 3,000 and 4,000 I/O points, says Jack Gourley, a regional engineering manager for Concept Systems.
MartinCSI, a CSIA Certified Member, works with all major PLC/PAC hardware/software solutions.
“We don’t look at solutions at per point or cost basis,” says Bill Sellitto, vice president of engineering. “We look at what I/O is required and find the type of module that will support that. When selecting processing power, we first look at what is required for the solution, then we look at the client’s budget and any manufacturer preferences. A majority of the hardware is rated the same if it is in an enclosure unless I/O is located out on a machine. Then we select hardware that is rated for the environment.”
When you think of Festo, besides I/O, you probably think of actuators controlling, for example, packaging machines. But again, scalability is the operative word in creating flexible machine designs. Festo offers both IP20 and IP65/67 controller solutions, says Sandro Quintero, product marketing manager, electric automation. One of them is the CPX platform that allows a centralized, decentralized or hybrid installation approach, depending on the machine architecture. The CPX platform is also recognized for its scalability, allowing users to add or remove modules according to their needs.
One of the best features of the CPX platform is its potential integration to valve manifolds, says Quintero. By using a pneumatic interface, a valve manifold can be attached to the CPX platform; this is ideal for central or hybrid installations. There is the potential to have up to 512 inputs and outputs on a single CPX terminal. The CPX terminal can be used either as a standalone terminal by having a CPX-CEC controller or as a slave in a network, such as EtherNet/IP, PROFINET, EtherCAT, among others.
The programming software used in CPX controllers is CODESYS, which follows the IEC 61131-3 industrial programming standard. This means users will be able to program in standard languages, such as Ladder, Structured Text, Sequential Function Chart or Function Block Diagram.
From single points of I/O to thousands, Rockwell Automation provides a wide range of PACs and control systems for connectivity across a plant floor, says Dennis Wylie, global product manager.
“In recent years, we’ve seen some changes in what food and beverage manufacturers need from their control systems. For example, cybersecurity needs are changing as increased connectivity and data-sharing can make systems more vulnerable to cyber threats,” says Wylie. “Rockwell Automation is designing strong cybersecurity into its control systems as much as possible and increasing its involvement in industry alliances to help all manufacturers improve cybersecurity. Another change we’re seeing is an increasing need for PACs that can withstand abusive environments.”
Rockwell Automation continues to offer more PACs that are designed for those harsh environments and can be mounted on machines (rather than inside a control cabinet) to save valuable plant floor space, adds Wylie.
Siemens provides an extensive portfolio of controller (PLC) offerings, ranging from the basic brick controller with a few hundred I/O points at the low end, all the way through its advanced controller lines that can handle tens of thousands of I/O points, says Jim Wilmot, marketing manager, SIMATIC PLC, I/O, software. The advanced controllers are available in a standard modular PLC design, PC-based software versions, and also in special form factors optimized for distributed configurations with different IP ratings—IP20 or IP65/67—for field mounting without a cabinet. All lines use the same programming tool, the TIA Portal, which makes scalability between the different lines simple; engineers write code once and can easily scale between the different hardware offerings as the application dictates, saving time and money for engineering.
As you can see, I/O count isn’t everything. Cybersecurity, environmental conditions and programming techniques are just as important. Arun Sinha, Opto 22 director of business development, suggests looking far beyond I/O count. “Look at the process, asset or machine to be used for the proof-of-concept, starting with sensors and instrumentation, then move to controller and I/O, including the software and tools required for real-time data processing at the edge. Next, consider IT-friendly protocols to move data outwards and possibly ‘upwards.’ Finally, explore what software, cloud services or tools are available to do more advanced analytics on the data.”
Does the OS matter?
The use of an internal real-time operating system (RTOS) within a PLC is pretty much a given. But there has always been the question: Should a PLC maker use a Windows derivative, a commercial RTOS kernel (today, VxWorks is popular), Linux derivative—or roll its own? If I/O count and processing complexity/capabilities are large, a PLC company isn’t likely to roll its own from scratch. Windows-based kernels (beginning with Windows CE and current Windows 10 derivatives) certainly provide a wealth of known programming tools, but so do VxWorks and Linux-based systems, which often use CODESYS, typically a free set of programming tools meeting IEC 61131-3 specifications.
“Bosch Rexroth controllers use VxWorks for the internal real-time operating system, and we provide an SDK, our Open Core Interface, for connection to other PCs or controllers,” says Tubbs. Using this approach, the controller can be optimized for real-time control. Traditional operating system tasks, like HMI control or data evaluation, still take processing power in a non-real-time environment. Depending on requirements, multicore processors can be used to split up tasks between the RTOS and, for example, a GUI.
“For our real-time deterministic controls, we use vxWorks RTOS,” says Vibhoosh Gupta, Emerson senior product manager. “Our outcome-optimizing controls use RTOS, while a second Linux operating system simultaneously runs machine learning and analytics algorithms to optimize the processes over a virtual network interface connection. OPC UA enables the two operating systems to securely communicate.”
“We employ primarily Microsoft Windows due to the fact that it’s more supported when it comes to IT, and customers tend to prefer it because it’s familiar to them,” says Concept Systems’ Gourley. “We sometimes use Linux, but only for very custom jobs.”
Likewise, Carlo Rodriguez, staff engineer at MartinCSI, reports that most of his clients use the Windows IoT OS and sometimes Linux ARM for edge devices, but usually there isn’t more than one OS in a single box.
Opto 22’s groov EPIC runs a real-time, open-source Linux custom Yocto build as a single OS supporting all necessary control, says Sinha. The build is cryptographically signed by Opto 22 for security.
Siemens’ Wilmot says, “The operating systems we use within our controllers vary dramatically depending on product line. Some are proprietary, others use Windows, Linux, or even have options for using virtual machines as well.” Therefore, a huge customer benefit offered by the SIMATIC controllers is flexibility. For some models, users can specify Windows or Linux. For other models, the controller runs a RTOS, and the main system can run Windows or Linux independently. Most important, with an independent RTOS and Windows operating together, should the Windows system “blue screen,” an engineer can reboot Windows, and the RTOS controls keep on running.
Cybersecurity matters
Obviously Windows has not had a great track record when it comes to cybersecurity, but much of the blame should go to Windows users who do things like not keeping the OS up to date, using easy-to-guess passwords or falling for email trickeries. Fortunately, PLCs, PACs and IPCs are much better protected—but then they need to be, otherwise there would be more Stuxnet-like events. So, I asked PLC/PAC makers how they protect their devices.
AutomationDirect’s Dehner suggested four security measures used in the BRX platform:
- Guest memory: A group of internal memory blocks are reserved for communications to external devices like operator panels and HMIs, but the memory is isolated from memory being used to run control applications.
- Session-based communications: When a session is established with a programmer, the session receives a unique ID, and it is only good for the length of time the programmer is connected. After signoff, the session ID is no longer valid for any user—period.
- Write-protected OS: As it sounds, but firmware downloads can be disabled, keeping unwanted OS changes from happening without operator intervention.
- Passwords/user accounts: Levels of access, event log messages allow complete tracking and control of users.
Another method that can help protect the security of the operating program is to use compiled code—rather than source code, says Bosch Rexroth’s Tubbs. This prevents a user from logging in and making random changes to the PLC program, while also providing a way to document changes to the source code. In addition, for machine builders and SIs, compiled machine code protects the intellectual property (IP) of the developer of the system as casual interlopers can’t read compiled code, which looks like gibberish. For example, look at any .exe file with Windows Notepad.
For systems using CODESYS, Festo’s Quintero says this programming system provides user management, password protection, and both project and communication encryption, which also helps ensure IP security and integrity. CODESYS also offers add-ons, such as the CODESYS Security Agent.
You can’t go wrong with advice from the Department of Homeland Security, and Emerson’s Gupta recommends the agency’s seven defense-in-depth (DiD) strategies. These include: (1) Build a defendable environment, (2) Reduce attack surface area, (3) Manage authentication, (4) Implement secure remote access, (5) Monitor and response, (6) Implement application whitelisting, and (7) Ensure proper configuration/patch management.
Siemens’ Wilmot suggests using highly encrypted password protection of blocks and copy protection for memory cards. Regardless of the amount of protection in the PLC, however, Wilmot emphasizes that manufacturers need to adhere to the DiD principles.
Adhering to published security standards means a PLC company is serious about cybersecurity. For example, Rockwell Automation announced earlier this year that the Allen-Bradley ControlLogix 5580 controller was the world’s first PAC to be certified compliant with the IEC 62443-4-2 security standard for industrial automation systems. The certification by third party TÜV Rheinland confirms the controller meets the global standard’s robust cybersecurity requirements. These include user identification and authentication (so only authorized users can access the system), continuous monitoring and logging, and integrity checks to help ensure the product has not been altered.
Secure networking
Keeping network traffic where it belongs is requisite to protecting controls networking, and one way to keep outside hackers on the business network away from PLC/PAC traffic is to create an industrial demilitarized zone (DMZ).
Nate Kay, project manager at Martin CSI, explains. DMZs, used in many IT applications, allow for secure mobile access to industrial control systems (ICSs). DMZs maintain isolation between the private controls network and the public-facing enterprise network. They allow the two networks to communicate through a firewall or another controlled access point.
Instead of merging controls equipment directly onto the enterprise network or giving the equipment direct internet access, an industrial DMZ can be set up by using devices, such as edge-of-network gateways, proxy computers, and virtual private networks (VPNs), to allow for secure and controlled access with mobile devices. Mobile devices and other public facing devices can then access information about the control system through the DMZ. DMZs also can incorporate security features—such as encryption—using protocols like transport layer security (TLS) and secure sockets layer (SSL)-based security.
Beyond secure vertical communications to the cloud using protocols such as OPC UA, AMQP and MQTT, controllers can benefit with secure communication horizontally at the fieldbus level, says Beckhoff’s Reiner. For example, the EtherCAT industrial Ethernet offers built-in security features—for example, unrecognized frames within a message will be ignored. Thus, data injected by a bad third party will be treated as garbage and thrown out, preventing damage to the network and its devices.
Rockwell Automation uses EtherNet/IP when connecting to outside networks, and new ODVA (Open DeviceNet Vendors Association) security enhancements such as CIP Security, create a more robust level of protection in control applications by making sure information is exchanged between authenticated devices, without interference or theft, says Rockwell’s Wylie.
Siemens uses PROFINET and OPC UA for communication and recognizes that industrial security plays an essential role in plants, especially with the increased connectivity within factories, says Wilmot. At the automation cell level, risk mitigation can be achieved by network segmentation access control to the automation cell and is secured by firewalls. Various automation cells are usually in a secured zone—which is separated from the unsecured zone via a DMZ, and traffic between the networks is protected by a firewall. Besides adhering to IEC 62443 Standards, secured communications like open user communication (OUC) can be achieved by using transport layer security (TLS).
I/O: Flexibility is key
Most controls vendors who’ve been around for a while know a variety of I/O types and form factors are necessary to meet today’s automation requirements. Emerson’s Gupta sees a continually expanding portfolio. For example, distributed slice I/O, chassis-based local and remote I/O configurations are available in a range of form factors, with feature sets and prices to fit any application. Common features today include hot-swap capability, real-time health monitoring and diagnostics. Like most PLC/PAC suppliers today, the Emerson I/O portfolio already supports more than one industrial I/O system—PROFINET, MODBUS and TCP—but also is adding protocols in the future, for example EtherCAT and EtherNet/IP.
While AutomationDirect has all the usual I/O that you would expect of a PLC/PAC supplier, it also has, according to Dehner, controllers with no I/O that can be used just for data logging or protocol conversion to controllers that are scalable up to 59,000-plus I/O points. But Dehner thinks analog signal wiring to field devices will eventually become obsolete as Ethernet becomes pervasive in device networks.
Festo currently supports digital, analog, IO-Link and HART outputs, but according to Quintero, is expanding to a new platform that will allow users to expand significantly their I/O—this is expected by the end of this year.
From a system integrator perspective, MartinCSI’s Sellitto says his firm has worked with all types of I/O, discrete, thermocouple modules, analog, IO-Link blocks, and he sees IO-Link as gaining popularity and being supported by more manufacturers.
Plug-and-play, a term associated with the computer industry, has been expanded to I/O modules, as Opto 22’s Sinha describes. The company’s groov EPIC I/O modules are smart in that they are automatically recognized by the controller and are also hot-swappable. The modules also include a touch-sensitive pad that brings up the module’s information on the onboard color touchscreen, allowing the user to configure, troubleshoot and force values, as well as bring up wiring diagrams, module specifications, etc. In addition, discrete modules—besides offering off-on capabilities—can be programmed for functions like counters, latches and watchdog timers.
The IIoT question
This article was not meant to be an IIoT piece. However, I did ask each of our experts for thoughts about PLCs, PACs and IPCs fitting into an overall IIoT networking strategy. You can read their responses to my question in a piece entitled, “PLCs, PACs and IPCs: Skip the IIoT acronym and get on with business.”
One new buzzword on the market is “TSN” (time sensitive networking), which is a new collection of IEEE standards that adds some nice advantages to Ethernet communications, says Siemens’ Wilmot. This will have some positive effects on PROFINET, which include improved robustness for higher network loads, scalable bandwidth (100 Mbit, Gbit), easier implementation of PROFINET devices—and it will allow standard Ethernet chips for isochronous applications. TSN will take some time to roll out but will be a positive change moving forward.
Today, with the range of controllers and I/O devices available, it would be all but impossible not to find one for your application. However, most importantly, there is no substitute for adequate planning so your system can grow with your needs.
For more information:
AutomationDirect, www.automationdirect.com
Beckhoff Automation LLC,www.beckhoffautomation.com/IPC
Bosch Rexroth Automation & Electrification Solutions, www.boschrexroth-us.com/automation
Concept Systems, www.conceptsystemsinc.com
Emerson, www.emerson.com
Festo Corporation, www.festo.us
MartinCSI, www.martincsi.com
Mitsubishi Electric Automation, https://us.mitsubishielectric.com/fa/en
Opto 22, www.opto22.com
Rockwell Automation, www.ra.rockwell.com
Siemens/Digital Industries, Factory Automation, www.siemens.com/plc
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






