Food Safety
VACCP: HACCP for vulnerability assessments
Vulnerability Assessment and Critical Control Point applies well-understood HACCP principles to protect food and beverage products from fraud and adulteration.

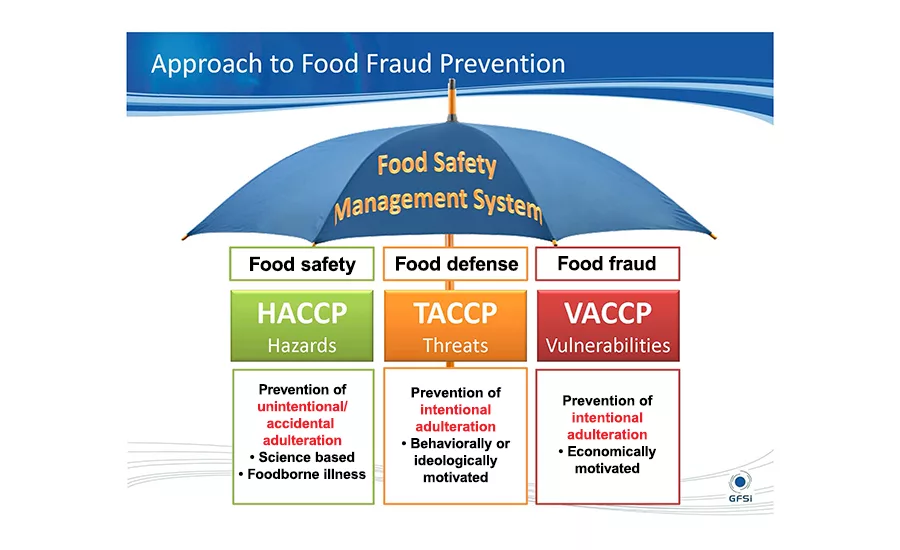
When the new GFSI Version 7 guidance document is released this year, the recommended food safety management system will consist of HACCP-based rules applied to food safety, food defense and food fraud. Source: John Spink, Food Fraud Initiative, MSU.

Food fraud has an impact on food quality, food safety and food defense, especially if the fraud affects people’s health. The GFSI Version 7 guidance document will include coverage on food fraud and vulnerability assessments. Source: GFSI.
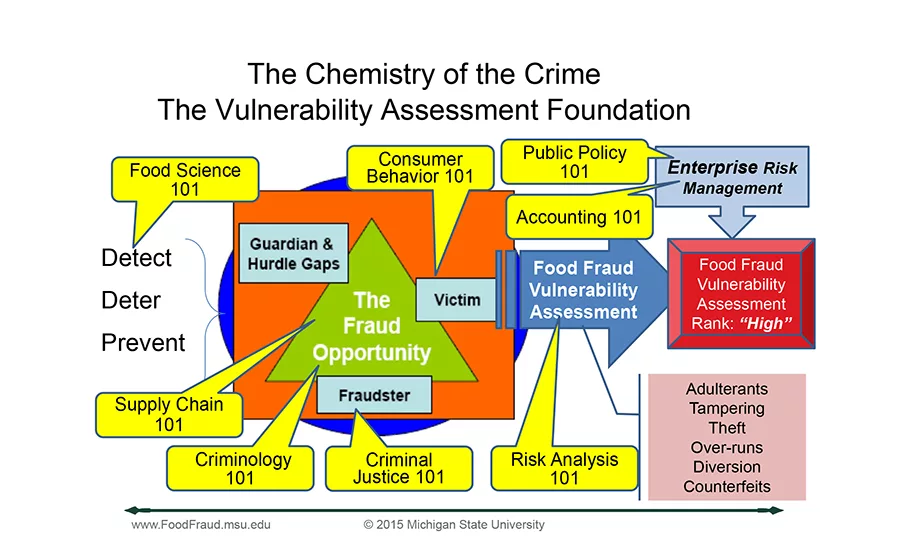
Finding a solution to prevent fraud requires input from experts in many areas. Source: John Spink, Food Fraud Initiative, MSU.
Endorsed by GFSI, VACCP (Vulnerability Assessment and Critical Control Point) is based on HACCP. It outlines a method to protect food and beverage products from fraud and potential adulteration, as opposed to intentional adulteration, which is covered by TACCP (Threat Assessment and Critical Control Point). Though VACCP is not covered specifically in FSMA, the ramifications of food fraud/adulteration can spill over into food safety concerns, for example, the Peanut Corporation of America incident or the melamine/pet food poisonings a few years ago.
Article Index:
Though FDA mentions the TACCP acronym just once, FDA’s FSMA covers intentional adulteration (threats) in its “Focused Mitigation Strategies To Protect Food Against Intentional Adulteration” rule, which becomes final in May 2016. TACCP refers to internal or external intentional, malicious contamination of food. GFSI will cover both VACCP and TACCP in Version 7 of its 2016 guidance document.
Note the operative word, “intentional,” which is what FSMA uses to address adulteration that could affect the health of consumers. At this point, unless food safety is affected, FSMA doesn’t have much to say specifically about VACCP, vulnerability and food fraud as they are more related to supplier/business issues/incidents and are covered by the FD&C Act.
VACCP: What is it, exactly?
Simply put, “VACCP is applying the HACCP-type system specifically to the unique attributes of a food fraud incident,” according to John Spink, assistant professor and director of the Food Fraud Initiative (FFI), Michigan State University. A vulnerability is a state of being that could lead to an incident. For example, GFSI defines food fraud, including the subcategory of economically motivated adulteration (EMA), as “the deception of consumers using food products, ingredients and packaging for economic gain and includes substitution, unapproved enhancements, misbranding, counterfeiting, stolen goods or others.”1
Related Articles
VACCP is unlike food defense, which is covered by TACCP and protects against malicious tampering to cause harm. The danger of food fraud comes from the fraudster’s potential inexperience with handling food products, for example, accidental spoilage, contamination or unknown contents.
Spink and his colleague, Doug Moyer, cofounders of MSU’s Food Fraud Initiative, considered some changes in thinking about food fraud. “Due to our previous corporate training, we felt we needed to get to the root-cause analysis and eliminate the potential for an [incident] to occur,” recalls Spink. “And, that was a key point where we realized we were shifting from risk to vulnerability. Risk is something that has occurred before, will occur again and has occurred at such a frequency you can actually measure it and predict its probability analytically. Vulnerability is the exposure to a risk, whether it’s happened before or not. For instance, if you leave a window open in your home, you’re more vulnerable to a break-in than if you close your window, even if no one’s broken in before.”
In July 2012, the Food Fraud Initiative participated in a GFSI Food Fraud Think Tank in an effort to establish methods to prevent food fraud occurrences, especially the types that make people or animals sick. “The goal is not to catch the fraudulent product, but to put in place systems that will prevent it from being in the system [supply chain] in the first place,” says Spink.
FSMA, HACCP and VACCP
“FSMA covers only part of the food fraud spectrum,” states Jim Cook, SGS North America food scientific and regulatory affairs manager. “VACCP and TACCP cover the entire food fraud spectrum.”
For example, VACCP isn’t anywhere in FSMA’s "Current Good Manufacturing Practice, Hazard Analysis, and Risk-Based Preventive Controls for Human Food" document. And, there are no references to “food fraud.” However, there are references in the document to EMA: “We [FDA] continue to believe that hazards that may be intentionally introduced for economic gain will need preventive controls in rare circumstances, usually in cases where there has been a pattern of economically motivated adulteration in the past. Economically motivated adulteration that affects product integrity or quality, for example, but not food safety, is out of the scope of this rule.”
Later in "Risk-Based Preventive Controls for Human Food" document, Response 402 stresses EMA is out of the scope of FSMA, unless people are sickened: “We [FDA] define hazards to only include those agents that have the potential to cause illness or injury. Economically motivated adulteration that affects product integrity or quality, for example, but not food safety, is out of the scope of this rule. We continue to believe that there is benefit in taking this preventive approach to economically motivated adulteration, and not solely on enforcing the preexisting misbranding and adulteration provisions of the FD&C Act after a violation occurs.”
Where FSMA and GFSI differ
GFSI’s Food Fraud Think Tank states mitigating food fraud, and any harm these incidents may cause to public health, requires a different perspective and skill set than those necessary for food safety or food defense as described in FSMA. Socioeconomic issues and food fraud history are not included in traditional food safety or food defense risk assessments. In addition, vulnerabilities related to food fraud can occur outside the traditional manufacturing, processing or distribution systems of a food company, according to GFSI’s position paper.
The Think Tank recommends two courses of action for the food industry to mitigate food fraud. First, processors should conduct a food fraud vulnerability assessment. In it, they should collect information at the appropriate points along the supply chain and evaluate it to identify and prioritize significant vulnerabilities for food fraud. Second, they should ensure appropriate control measures are put in place to reduce the risks from these vulnerabilities. These measures may include a monitoring strategy, testing strategy, origin verification, specification management, supplier audits and anti-counterfeit technologies.
Spink and Moyer believe the analysis will determine if there are hazards and, if so, which require preventive controls. To be consistent with the European Commission, the UK and GFSI, this would be a “vulnerability assessment.” However, there is some confusion because FDA refers to a food defense risk analysis as a “vulnerability assessment,” according to FFI’s report.2
Spink and Moyer take issue with the word "facility" in the FSMA rule since this typically refers to an interior plant, and food fraud, vulnerability and root cause generally occur outside a single facility. Thus, a “facility subject to the rule” could have a food fraud vulnerability assessment and control plan (FSMA, Comment 403) tailored specifically to EMA administered by a central enterprise-wide location such as corporate headquarters.
What’s in the Preventive Controls rule regarding food fraud and EMA is open to interpretation, but that doesn’t absolve processors from responsibility. “What it says is that it’s up to you to define whether there is a hazard or not, and if you decide there is, you must have a preventive plan in place,” explains Spink. “That puts a lot of [onus] on the risk assessor. The bottom line: If there’s an incident, your product is going to get recalled, no matter how that incident occurs. The food, drug and cosmetic law is still in effect. And, you might have the greatest prevention plan in the world, but if you have horsemeat in your beef, that product is still getting recalled.”
Processors should ensure they meet their respective GFSI certifications (e.g., BRC, SQF or FSSC). If they do, they will be in good stead with FDA and FSMA. “If they do GFSI, they technically at this point [until we have additional insight from FDA] will meet the FSMA compliance for EMA and food fraud,” says Spink.
“It would be advantageous for US facilities to adopt the process of threat and vulnerability assessment to assess food fraud and/or adulteration to protect their business, their brand and their consumers,” advises Kassy Marsh, Techni-K director. “No doubt, it will become part of the GFSI standard, given GFSI has invested so much in the Food Fraud Think Tank’s work and the success of the implementation of the requirement to the BRC V7. I would recommend US food facilities invest in one type of threat and vulnerability assessment, which will meet the GFSI [BRC] requirements of the food fraud element for raw materials and the process-driven assessment to meet the requirements of FSMA.”
Coming together
GFSI has been beefing up guidance on both intentional adulteration and food fraud/EMA, and its diagram (shown above) on food fraud shows how closely linked food quality, food safety, food fraud and food defense are. Guidance in the next Version 7 document will no doubt show the convergence of all these elements pertaining to safe, high-quality food products.
However, for the present, some confusion remains. To address this issue, Marsh’s firm provides training and educational materials on VACCP and TACCP in the UK, and fields questions from food and beverage processors seeking actionable information. “I get asked all the time what the difference is between TACCP and VACCP. There have been many mixed messages and explanations as to what they are and which should be applied to what situation.”
Adding to the confusion are the CCPs. “Both TACCP and VACCP refer to critical control points,” adds Marsh. “But neither methodology explains how to determine the critical control points or how they should be managed.”
“In my opinion, TACCP and VACCP are fundamentally linked,” continues Marsh. “TACCP is obviously all about threats, acts carried out by someone to cause harm or loss. VACCP refers to vulnerability, which is how exposed a company is to a particular risk, such as a threat or a hazard. Therefore, I believe rather than TACCP or VACCP, we should be referring to a ‘threat and vulnerability assessment’ that determines which threats a business or consumer is vulnerable to.”
Marsh points out three degrees of vulnerability in a typical food fraud situation in the following example:
Horsemeat is being delivered to your site instead of beef due to fraudulent activity in the supply chain:
- If the meat is delivered minced, there is no easy visual indication as to what type of meat it is, so you’re vulnerable.
- If the meat is delivered as a joint, you are less vulnerable as you can probably recognize the joint doesn’t look like beef.
- If the meat is delivered as a carcass, you’re definitely able to recognize it’s not beef, so you’re not vulnerable.
The concept of a threat and vulnerability assessment makes sense, but processors will have to determine the likelihood of intentional contamination because in most cases, food fraud will not result in contamination. Food fraud is a business, which like any food business, doesn’t want sick customers—or the fraudsters have no outlet for their “product.”
In fact, PAS 96:2014, “Guide to protecting and defending food and drink from deliberate attack,” published by the British Standards Institute, makes no distinction between EMA or food fraud and intentional contamination and identifies them all as threats. Though the guide covers TACCP in detail, including assessing vulnerabilities and risks and setting up critical controls, it makes no specific reference to VACCP.
VACCP tools
Help is available for anyone concerned about food fraud. For instance, the U.S. Pharmacopeial Convention’s “Appendix XVII: Food Fraud Mitigation Guidance” which can be used as an informational tool and resource. Section A, “General Guidance for Food Ingredients,” provides guidelines for developing and implementing a preventive management system to deal specifically with the intentional, economically motivated, fraudulent adulteration of food ingredients. It provides a qualitative, structured approach divided into four major steps for carrying out ingredient-by-ingredient assessments.
SSAFE (www.ssafe-food.org) has worked with GFSI in addressing food fraud. It has also worked with the University of Wageningen RIKILT to create a free tool to help processors perform a food fraud vulnerability assessment and prepare a control plan, irrespective of the geographic location, size or type of food operation. According to Professor Saskia van Ruth, professor, food authenticity and integrity at Wageningen University and Research Centre, the e-tool is available at www.pwc.com/foodfraud.
The e-tool is being released by PwC; SSAFE is also placing the Excel version on its website. “This tool is designed for intentional adulteration and contamination, which are economically driven, but not for cases that are ideologically driven [where the motive is harm],” says van Ruth. “We identified 50 risk factors in the categories of opportunities, motivations and control measures,” adds van Ruth. “We considered different environmental layers, [food] companies, direct suppliers and customers, the wider supply chain network and the international [and national] environment.”
Next month, Food Engineering will provide details on TACCP.
For more information:
Jim Cook, SGS North America, 973-461-1493,
james.cook@sgs.com, www.sgs.com
Kassy Marsh, Techni-K, 01909 511252,
kassy.marsh@techni-k.co.uk, www.techni-k.co.uk
John Spink, Food Fraud Initiative, MSU, 517-381-4491,
spinkj@msu.edu, www.foodfraud.msu.edu
References:
- GFSI Position on Mitigating the Public Health Risk of Food Fraud, July 2014, www.mygfsi.com/files/Technical_Documents/Food_Fraud_Position_Paper.pdf.
- FFI Report: “Review—Final Rule for FSMA Preventative Controls Regarding Food Fraud and EMA,” Spink and Moyer, MSU FFI , Oct. 8, 2015, http://foodfraud.msu.edu.
Resources:
The Food Fraud Initiative,
http://foodfraud.msu.edu.
“GFSI Direction on Food Fraud and Vulnerability Assessment (VACCP),”
John Spink, May 8, 2014, Blog.
United States Pharmacopeial Convention,
“Appendix XVII: Food Fraud Mitigation Guidance,” 2015.
SSAFE,
www.ssafe-food.org.
CARVER + Shock Primer: AN OVERVIEW OF THE CARVER PLUS SHOCK METHOD FOR FOOD SECTOR VULNERABILITY ASSESSMENTS; FDA 9/2009.
“Focused Mitigation Strategies To Protect Food Against Intentional Adulteration,”
FDA Proposed Rule (Federal Register).
“GFSI Position Paper on Mitigating the Public Health Risk of Food Fraud,” 7/14/2014
MyGFSI, July 2014.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!