Food Safety
TACCP: HACCP for threat assessments
Threat assessment and critical control point applies well-understood HACCP principles to protect food and beverage products from intentional and malicious contamination.

PAS96:2014, Guide to protecting and defending food and drink from deliberate attack, applies TACCP principles to both intentional and unintentional adulteration/food fraud activities. The document can be downloaded for free. Source: British Standards Institution.

In the GFSI food safety management system, TACCP, or food defense, deals with the prevention of intentional adulteration, whether behaviorally or ideologically motivated. Source: John Spink, Food Fraud Initiative, MSU.
Nanjing, China, September 18, 2002: “Police have arrested a snack bar owner who confessed to spreading lethal rat poison into the food of his business rival on Saturday morning, killing 38 people and leaving hundreds seriously ill.”—China Daily.
The Dalles, OR, September 17, 1984: “A Large Community Outbreak of Salmonellosis Caused by Intentional Contamination of Restaurant Salad Bars.” This incident highlights the challenge of investigating outbreaks caused by intentional contamination and demonstrates the vulnerability of self-service foods to intentional contamination.— JAMA, August 6, 1997—Vol. 278, No. 5, (PDF) CDC website.
Article Index:
Of the two stories above, the first was motivated by the perpetrator’s jealousy of a rival snack bar operator; the second was caused by a religious sect intent on disrupting local elections in a small town in Oregon. However, in today’s climate of worldwide terrorism, threats to food products can happen anywhere along the supply chain—from agriculture to distributors, importers and ingredient suppliers to processors and their distribution networks—with varying effects to the public.
The USDA FSIS paper, “Developing a Food Defense Plan for Meat and Poultry Slaughter and Processing Plants,” focuses on how to protect the food supply from intentional contamination with a variety of chemicals, biological agents or other harmful substances. These agents could include materials that are not naturally occurring or are not routinely tested. Intentional acts are generally not reasonable and are hard to predict. The FSIS paper lays the groundwork and provides worksheets for developing a food defense plan.
Threats—and how to mitigate their occurrence—to the food chain are covered extensively in documents such as the British Standards Institution PAS 96:2014 (Guide to protecting and defending food and drink from deliberate attack), GFSI Guidance Document Version 7.0, which is scheduled to be released this year, and FDA’s FSMA Final Rule, Focused Mitigation Strategies To Protect Food Against Intentional Adulteration, which becomes law in May 2016. (Although FSMA doesn’t deal extensively with Threat Assessment Critical Control Point [TACCP], it does address threat assessments, risk and vulnerability.)
PAS 96:2014 and GFSI, which follows PAS 96’s lead, define TACCP as the “systematic management of risk through the evaluation of threats, identification of vulnerabilities and implementation of controls to materials and products, purchasing, processes, premises, distribution networks and business systems by a knowledgeable and trusted team with the authority to implement changes to procedures.”
“The BRC [British Retail Consortium, a GFSI scheme owner)] defines TACCP as a ‘system to give a structured approach to the assessment of the security of food and drink in relation to malicious contamination and food fraud,’” says Jim Cook, SGS North America food scientific and regulatory affairs manager.
“TACCP is a risk management methodology that aligns with HACCP, but it has a different focus that may need input from employees from different disciplines, such as HR, procurement and/or security,” offers Greg West, International Accreditation Service (IAS) marketing manager. “TACCP also complements existing business risk management and incident management processes. Examples of food threats under TACCP include malicious contamination, economically motivated adulteration, extortion, espionage, counterfeiting and cybercrime.”
What FSMA says about TACCP
FDA has concluded a preventive controls approach like the one used for the systematic control of food safety hazards in the FSMA Preventive Controls Rule is the most effective means of reducing the risk due to intentional adulteration. However, during the comment period, FDA was also looking for outside input on HACCP-style controls for ensuring food defense.
According to FDA, “The application of HACCP-type controls for ensuring the implementation of food defense mitigation strategies is consistent with the approach taken in Publicly Available Specification (PAS) 96. It is also consistent with WHO recommendations on protection against intentional adulteration.”
Related Articles
In addition, FDA suggests certain food/beverage operations are covered by Section 418 (HARPC) and/or Section 420 (Protection against intentional adulteration) of the FD&C Act. According to FDA, applying the same regulatory framework under these sections would facilitate a concise, consistent approach for protecting against the intentional adulteration of food and the efficient enforcement of the requirements. Furthermore, this approach would be consistent with the one for unintentional adulteration that many facilities would already be required to use for unintentional hazards under the preventive controls (PC) rule.
FDA recognizes regulating entities in the food production system to reduce the risk of intentional adulteration of food caused by acts of terrorism is basically without precedent. Such an endeavor is complicated by the low probability and potentially high impact of such an attack, which makes establishing potential health benefits and an appropriate threshold for action difficult. Finally, FDA tentatively concludes a hazard-analysis type approach is better suited to address economically motivated adulteration than the vulnerability assessment-type approach it is proposing to address intentional adulteration related to terrorism.
TACCP in Europe
PAS 96:2014 covers threats or hostile acts to the food supply (food defense), as well as non-threatening acts such as food fraud. It also describes the characteristics of the main threats to food authenticity and safety—economically motivated adulteration (EMA) and malicious contamination—and outlines the nature of other threats, such as extortion, espionage, counterfeiting and cybercrime.
PAS 96:2014 divides attackers into seven personality types. The extortionist wants financial gain, but doesn’t want to be caught, while an opportunist could hold an important position within the operation and be able to evade internal controls. The extremist takes his or her cause seriously and may want to cause harm while enjoying the subsequent notoriety. The irrational individual may have mental health issues, while a disgruntled individual believes an organization has been unfair and seeks revenge. Hacktivists and other cybercriminals subvert controls on computer systems to stop their operation, steal information or corrupt data. The professional criminal may see food fraud as a relatively simple crime with big gains and little chance of apprehension.
Processors can use TACCP as part of a broad risk management program to reduce the likelihood of a deliberate attack; minimize the impact of an attack; protect their organization’s reputation; reassure customers, press and the public they have steps in place to protect food; satisfy international expectations and trading partners; and demonstrate they are exercising precautions and due diligence to protect food.
TACCP identifies specific threats to a company’s business; assesses the likelihood of an attack by considering the prospective attacker’s motivation, the vulnerability of the process and the capability the perpetrator has of carrying out the attack; assesses the potential impact; judges the priority for different threats; decides on proportionate controls to discourage attackers; and maintains information and intelligence systems to enable the revision of priorities.
PAS 96:2014 provides pointers on setting up a TACCP team and assessing threats, vulnerabilities and risks. It also looks at the role of critical controls in risk reduction, tamper detection and personnel security, as well as how to respond to a food protection crisis and plan for recovery from an attack. In addition, the document provides case studies showing how TACCP can be applied.
“A monitoring system needs to be put in place to control both internal and external operations for the identified threats,” explains West. “All critical parameters must be under close surveillance, and actions must be taken as necessary. Internal audits and second-party audits are two of the tools that can be used for [threat assessment].”
CCPs—What you should be doing
“According to the HACCP concept, a critical control point [CCP] is applied to a ‘point’ in the process where the identified hazard can be definitively controlled,” says Felix Amiri, technical director for Canadian-based Amiri Food Industry Support Services (AFISS). On the other hand, Codex defines a CCP as “a step at which a control can be applied and is essential to prevent or eliminate a food safety hazard or reduce it to an acceptable level,” adds Amiri.
Cook points out a couple of examples where the point is easily defined and controlled in VACCP. “A CCP in VACCP is the specific point, procedure or step in the supply chain or process at which a control can be exercised to reduce, eliminate or prevent the possibility of economic fraud. This CCP could be a DNA species analysis on red snapper to verify there has been no substitution, justifying the premium price. Another item for a CCP could be ELISA peanut allergen testing on paprika to ensure no peanut/peanut water is in the paprika.”
To identify TACCP critical control points, PAS96:2014 states the TACCP team should look for potential threats (perform a threat assessment). For example, in terms of product, does it contain ingredients or other material sourced from overseas? Are large numbers of people (including the general public) entering the location? Do some people regard the brands as controversial? Which suppliers are not routinely audited? Do storage containers have tamper-evident seals?
PAS 96:2014 describes what it considers to be critical controls. For example, blocking access (via chip and PIN access control, CCTV monitoring/recording of perimeter vulnerabilities, screening visitors, etc.) can decrease risk. Similar measures can be applied to detect ingredient and product tampering.
The problem with vulnerability to both fraud and food defense/threats is that unlike a fixed process (e.g., pasteurization or sterilization) where the targets remain the same—unless the process changes—the control points are varied and tend to shift, says Amiri. “The best approach for dealing with shifting targets is to adopt the same kind of control measures strategy as the universally recognized prerequisite programs [PRPs] under HACCP. Control measures, rather than critical control points, are expected to be implemented to address detected threats and vulnerabilities. But, I see any attempt to identify CCPs for food defense threats or fraud vulnerabilities as an exercise in futility.
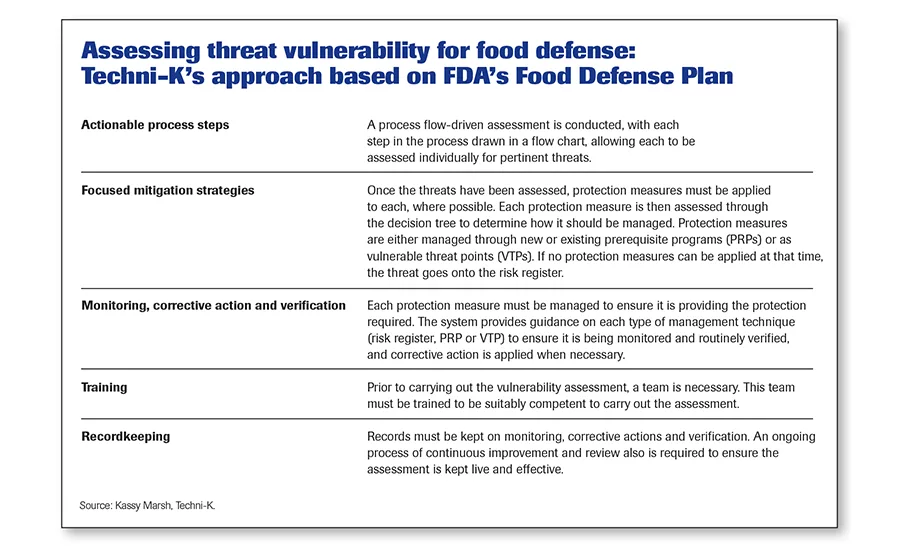
Amiri isn’t the only one having a problem with TACCP or VACCP. “In our opinion, none of the TACCP or VACCP guidance explains what CCPs are, how to determine them in an assessment or how to manage them once they have been identified,” says Kassy Marsh, Techni-K director, a consultancy based in the UK. “For this reason, we came up with a system that determines how we should protect ourselves against vulnerable threats, using ‘protection measures.’ Each of these measures is then assessed through a decision tree, and a management technique is determined which uses an existing or new PRP or as a vulnerable threat point (VTP). A VTP is a threat equivalent of a CCP.”
Can TACCP work with FSMA?
FDA has moved many processors from HACCP principles to HARPC (hazardous area, risk-based preventive controls) for food safety purposes. What about TACCP? “The TACCP idea is similar to the FDA rules in that both sets of requirements are proactive in nature,” says Amiri. “They expect a determination of possible threats of intentional adulteration with specific ‘control’ actions taken to mitigate these anticipated threats. They both place the onus of the threat determination and mitigation actions on the food business, although FDA also provides a tool [vulnerability assessment software] to assist operations.”
“FDA and TACCP both assess internal processes and systems to establish critical control points and procedures to prevent intentional adulteration,” says SGS’s Cook. “The US FDA proposal identifies four vulnerable operations [See sidebar below, “Four key vulnerable activities”] that must be considered. But, it also suggests looking at additional areas. To perform TACCP correctly, a supplier must search for potential threats across the entire supply chain, the external and internal operations. Like VACCP, TACCP includes a wider assessment than FSMA requirements.”
“TACCP assesses the pertinent threats within a given scope to highlight which have vulnerabilities,” says Techni-K’s Marsh. “The methodology we provide allows a threat and vulnerability assessment to be carried out as a process flow-driven assessment or by assessing raw materials or groups of raw materials prior to delivery.
“FSMA focuses directly on—and only on—intentional adulteration threats,” adds Marsh. “To comply with the act, food facilities must carry out a vulnerability assessment as part of their food defense plan.” The plan must include the following elements:
- Actionable process steps
- Focused mitigation strategies
- Monitoring
- Corrective action
- Verification
- Training
- Recordkeeping
“Unfortunately, typical TACCP systems do not cover all these elements and focus mainly on the risk assessments of the threats,” says Marsh. (The methodology Marsh uses is aligned to FSMA’s Food Defense Plan and is shown in the sidebar on this page, “Assessing threat vulnerability for food defense.”)
Applying TACCP for elusive threats
Planning for a possible terroristic threat is not an easy task. “Applying CCPs to intentional adulteration threats is a suggestion with the prospect of a prolonged confusion in the industry,” says Amiri. “It would be difficult, if not altogether elusive, to identify with any degree of certainty the critical points at which controls can be applied to prevent or eliminate malicious adulteration threats or reduce them to an acceptable level. Don’t forget these threats are created by subversive elements.”
According to Amiri, food processors need an organic (evolving and improving) strategy that matches the ever-changing tactics of subversive elements. “Proceeding with a CCP mindset may do no more than lead to wasted time searching for elusive points of control, or a deceptive and disarming assurance points of control have been established.”
However, that is not to say clearly vulnerable points shouldn’t be guarded. For example, in its proposed intentional adulteration regulation, FDA lists four areas of concern. Mixing is one of these.
“Evaluating the areas of concern and determining the critical points that control these areas or functions would prevent adulteration from occurring,” says Cook. “In all operations, mixing or blending is a critical control point. From a supplier perspective, the process is meant to specifically investigate the supply chain of those items that are more likely to be intentionally adulterated. Internal TACCP evaluation will help a facility comply with the FDA intentional adulteration rule. External evaluation strengthens the supply chain and, if done correctly, confirms the product or ingredient received will not cause harm. The overall benefit is the improvement of food safety and quality programs.”
“Protection measures that result in a VTP [vulnerable threat point, which is equivalent to a CCP] must be applied to ensure the food facility is not vulnerable to a threat,” says Techni-K’s Marsh. “Internal VTPs are the most robust, as they can be effectively managed and verified. However, VTPs passed on to a third party, such as a supplier, cannot be considered as robust since they are not within your control. Therefore, if a VTP is passed on, an alternative or additional protection measure should be considered, such as the unannounced testing of the product on delivery to ensure the supplier has adhered to the agreement.”
Food has been intentionally contaminated throughout history, but today, we can be better prepared to combat it.
“Food fraud has been a problem since humans first traded food with other humans,” says SGS’s Cook, “and bioterrorism has been used in warfare. But, the global economy that has been created in the last 20 years makes it apparent these problems, once isolated to a specific country or region, are now worldwide problems, and more controls are needed to combat them.
“VACCP and TACCP are structured approaches to prevent hazards from occurring,” adds Cook. “It is critical that suppliers and importers take a systematic approach not only to avoid excessive verification activities and control points, but to avoid having an insufficient program that provides no real value to themselves or the public.”
Four key vulnerable activities for intentional adulteration
The FDA Proposed Rule, Focused Mitigation Strategies to Protect Food Against Intentional Adulteration, identifies four key activities/operations within a food system that are most vulnerable to intentional adulteration. They include:
- Bulk liquid receiving and unloading
- Liquid storage and handling
- Secondary ingredient handling (the step where ingredients are handled before being combined with the primary ingredient)
- Mixing and similar activities
Facilities would be required to review their production system to determine if they have any of these activities or complete their own vulnerability assessment. Once an assessment is completed, processors would need to identify actionable process steps that will require focused mitigation strategies to reduce the risk of intentional adulteration.
Source: FDA.
Resources:
PAS 96:2014 (Guide to protecting and defending food and drink from deliberate attack), PDF download.
The Food Safety Modernization Act (FSMA), 2011,
www.fda.gov/Food/GuidanceRegulation/FSMA/ucm247548.htm.
“Assessing Threat Vulnerability for Food Defence,” Adele Adams and Kassy Marsh,
Techni-K, 2015, www.techni-k.co.uk/threat-vulnerability.
Focused Mitigation Strategies to Protect Food Against Intentional Adulteration, FDA, Dec. 24, 2013, PDF download.
“Developing a Food Defense Plan for Meat and Poultry Slaughter and Processing Plants,” Jan. 2007, Jan. 2008, http://www.fsis.usda.gov/shared/PDF/Food_Defense_Plan.pdf.
“Semper paratus! Food defense depends on it”, FE, May 2014.
“FDA releases new tool to help prevent intentional food contamination,” FDA, May 13, 2013.
“Intentional Food Poisoning,”
Jerrold B. Leikin, MD, Chicago Medicine, April 2014.
“Intentional Contamination: The Legal Risks and Responsibilities,” Denis Stearns, JD, Journal of Environmental Health, Vol. 70, No. 6, Jan./Feb. 2008, Marler-Clark website.
FDA Tools & Educational Materials
Food Defense Mitigation Strategies Database, FDA,
www.accessdata.fda.gov/scripts/fooddefensemitigationstrategies/.
For more information:
Jim Cook, SGS North America, 973-461-1493,
james.cook@sgs.com, www.sgs.com
Kassy Marsh, Techni-K, 01909 511252,
kassy.marsh@techni-k.co.uk, www.techni-k.co.uk
Greg West, International Accreditation Service, 562-364-8201,
gwest@iasonline.org, www.iasonline.org
Felix Amiri, Amiri Food Industry Support Services, 519-323-3515,
felix@afisservices.com, www.afisservices.com
John Spink, Food Fraud Initiative, MSU, 517-381-4491,
spinkj@msu.edu, www.foodfraud.msu.edu
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!