Cybersecurity
Cybersecurity helps manufacturers create more secure, resilient networks

Your intellectual property is at risk! The FBI issued this December 2018 poster showing Zhu Hua and Zhang Shilong, who were indicted for “extensive campaigns of global intrusions into computer systems to steal—among other data—intellectual property and confidential business information from more than 45 commercial and defense technology companies in at least a dozen states.”
Photo courtesy of FBI
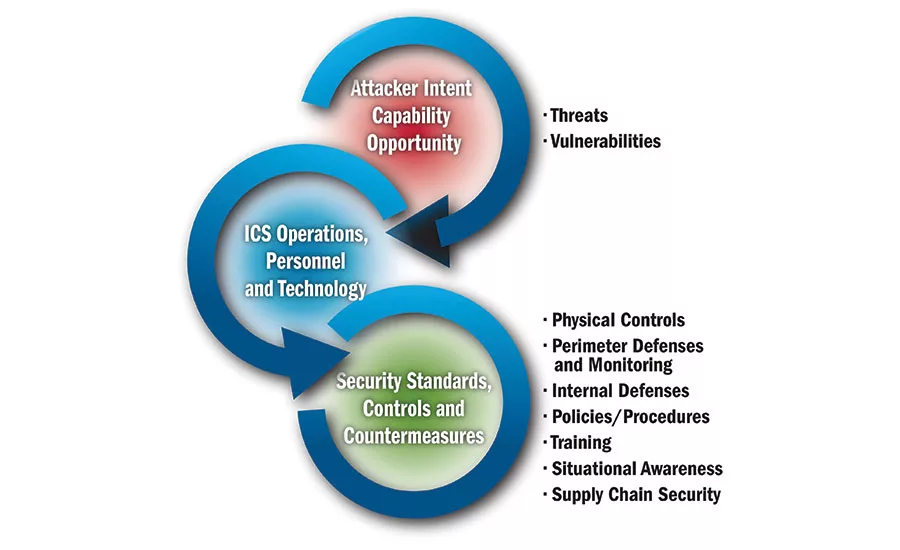
In order to apply defense-in-depth (DiD) to ICS environments, an organization must understand the relationship of intruders (threats) and vulnerabilities to the controls (standards and countermeasures) put in place to protect operations, personnel and technologies that comprise an ICS.
Chart courtesy of ICS-CERT

This secure architecture design is the result of an evolutionary process of technology advancement and increasing cyber vulnerability presented in the recommended practice document, “Control Systems Defense-in-Depth Strategies.” Online with this interactive schematic, you can hover over the various areas of the graphic and click inside each box for additional information associated with the system elements.
Chart courtesy of ICS-CERT

ICS-CERT recommends a zone segmentation of business and ICS architecture with a DMZ between enterprise and manufacturing—and a DMZ separating the enterprise zone from the internet.
Chart courtesy of ICS-CERT
If you know anyone who has a current state-of-the-art pacemaker, most likely it can be programmed via a Windows-based computer at the doctor’s office. Most pacemakers use near-field communications, which means they can only communicate with another device at a distance of 1 or 2 inches, making direct access difficult for a potential hacker.
However, the real issue is: What can be accomplished by breaking into the networked Windows host computer used to read or program the pacemaker? You can imagine the possibilities—or consequences.
Article Index:
And so it is with industrial devices, such as programmable controllers, motor drives, actuators and smart sensors. Any device connected to an industrial network and capable of being programmed or recalibrated by an infected Windows computer—either directly or through a Windows-based TCP/IP network—is at risk unless precautions have been taken. Don’t forget the Stuxnet worm that is thought to have damaged Iranian centrifuges.
If you think this is scary, you’re right. You need to be scared out of complacency and into taking action—because the very life of your business may depend upon how you respond to preventing potential cybersecurity attacks.
“Our dependency on connected technology is growing faster than our ability to secure it, and it’s affecting public safety and human life,” says Joshua Corman, chief security officer of PTC software company. He should know. He’s worked on several government cybersecurity projects and started the I Am The Cavalry website, which focuses on cybersecurity in public infrastructure, medical devices, automobiles and home electronics.
You’ve seen and heard about hacking incidents through the news, technical/trade journals and government websites. The worry is no longer the kid hacker who’s having fun—except when a “fun” project accidentally escapes into the wild and wreaks havoc with a corporate IT system. The real concern is with rogue nation-states and organized criminals who are betting that they can take down sensitive industrial control systems and utilities or get a huge ransom payout from a corporation with deep pockets.
In fact, two incidents have shown that opening a dam’s spill gate or shutting down a utility system is possible. And ransomware developed by at least one nation-state—presumed to be North Korea—affected Sony Pictures Entertainment, Lockheed Martin, a Bangladesh bank and several other companies.
Another believed to have been developed by North Korea, the widespread ransom-worm known as WannaCry affected 81 hospitals and their ability to provide patient care and emergency services. It later affected factories for Renault, Honda and others.
Think the food industry is safe from hacking? Ask Mondelēz, which experienced a cyberattack in 2017 with a negative impact to its earnings. “Cybersecurity doesn’t discriminate by industry,” says Laura Lee, executive vice president of rapid prototyping at Circadence, a provider of cloud-based cybersecurity training. “Hackers are on the lookout for any vulnerabilities in systems and networks with the intention to exploit, damage or destroy monetary information, data, infrastructure and company reputations.”
Separating ICS and business networks
At one time, plant SCADA or industrial control system (ICS) networks were totally isolated from higher-level and business networks, but isolated networks have evolved to a connected but segmented architecture for many facilities, where managers want to monitor the process, machines and associated equipment.
A lot of Rockwell Automation clients are beginning to understand that networks are more connected than ever, says Tony Baker, Rockwell portfolio manager, security. “Often manufacturers believe they have effective network segmentation, but after an assessment, they realize they don’t, and then must work frantically to improve.”
While the worry may be that a virus could enter the business network and traverse to the plant ICS, often the converse is true—a virus can enter the control system and wend its way upward to the business system. Think of Target stores, where an HVAC contractor unknowingly infected the business system through the HVAC controls where he connected his laptop.
“A lot of people still have the perception that the ICS is on the safe side of things, and you can be more liberal with security. Wrong!” says Steven Pflantz, CRB associate. “More and more focus is on the ICS and ways that third parties can come in and service the ICS. That can potentially be the point of intrusion, coming in from the outside, through the ICS and into the corporate network.”
“A lot of people still have the perception that the ICS is on the safe side of things, and you can be more liberal with security. ... More and more focus is on the ICS and ways that third parties can come in and service the ICS. That can potentially be the point of intrusion, coming in from the outside, through the ICS and into the corporate network.”
– Steven Pflantz, CRB
But segmentation can get a little more problematic than just separating the controls layer from business. “When we say ‘segmentation,’ we are referring not only to segmentation between the IT and OT (operations technology) networks, but also segmentation within the OT network environment (aka micro-segmentation, zones, etc.),” says Patrick McBride, chief marketing officer of Claroty, an ICS cybersecurity provider. “The former can make it harder for attackers to gain a foothold within the OT network, and the latter can make it much more difficult for them to move laterally if they do happen to gain access.”
Based on Claroty’s experience with hundreds of OT environments and network segmentation projects, network segmentation by deploying actual physical separation (VLANs) or logical isolation (firewalls) can require lengthy design and implementation periods, not only consuming significant staff time from both network operations and OT teams, but also requiring networks to be taken offline.
Best practices in ICS security
IT and OT convergence requires a holistic approach to industrial cybersecurity, extending from a single enterprise system to the people, processes and technologies within a plant, says Nick Boughton, digital lead at Boulting Technology, a cybersecurity consulting company stationed in the U.K. In a 2016/17 report, “The Cyber Threat to UK business,” the National Cyber Security Centre suggested cybersecurity is most effective with risk management procedures, Boughton points out.
“Manufacturers should first complete a risk analysis and discuss the balance between their business objectives and the risks they’re willing to take,” says Rockwell’s Baker. To maintain basic cyber hygiene, Baker suggests asking at least the following basic questions during a risk analysis: How do you navigate controls to implement the solutions? Who has access? What needs to be protected? How should it be used? Once users have access to the systems, what else do they have access to?
What else should risk management look like? According to Circadence’s Lee, manufacturers looking to protect the ever-converging IT and OT infrastructure need to:
- Identify and harden the critical assets, infrastructure and networks that are needed to continue operation during a cyberattack
- Employ basic secure coding principles
- Engage in persistent learning and skill-building efforts, using “virtual cyber ranges” to practice IT/OT cyberattack mitigation
- Establish a living configuration management program for software and hardware
In addition, Lee recommends manufacturers should conduct regular risk assessments and make equipment suppliers and contractors partners in securing systems.
A recent study performed by Indegy Labs found that 86 percent of those polled rated insiders as the biggest security threat to their organizations, says Michael Rothschild, Indegy senior director, product marketing. He adds a few more pointers to consider in risk assessments:
- Perform a risk assessment to identify and address vulnerabilities, such as over-privileged accounts, insiders with access to resources they don’t need to do their jobs, orphaned accounts belonging to terminated employees, contractors, etc.
- Know and monitor attack vectors. There are two primary vectors: using the network and targeting devices directly via serial ports. The latter occurs when a user plugs a device into an industrial controller to distribute malware, upload new code, etc. Serial attacks can propagate quickly and evade network-based passive detection mechanisms. Monitoring both network activity and device integrity is required to detect these two types of threats.
- Unify IT and OT security. Since both environments are often interconnected, an attack that originates on the IT network can move to the OT environment. Establishing visibility across both IT and OT networks by integrating security tools and the data they generate can help detect any unwarranted network activity.
Tools for the ICS or OT level
Whatever tools you decide to use—hardware or software—you should consider five elements to achieve the visibility, security and control needed to protect your SCADA network, says Indegy’s Rothschild. These include monitoring the following:
- Device integrity—OT protection that routinely queries devices in their native language for modifications made to their configurations, code and state. Device integrity also detects local changes made to devices and provides context to help understand the nature of an alert.
- Threat detection and mitigation—Combines behavioral anomalies with policy-based rules. Anomaly detection correlates network baseline patterns to identify suspicious activity, while policy-based rules provide granularity for discovery of changes that may not appear statistically significant.
- Asset tracking—Discovers dormant assets and data that are not active or discoverable in network traffic (e.g., Windows-specific versions, hotfix/patch level, etc.). Asset tracking presents full backplane configuration of devices to identify the ones with multiple controllers and network cards.
- Configuration control—Validates device changes made locally and/or over the network.
- Enterprise visibility—Integration of ICS security with commonly deployed IT security products, such as security information and event management (SIEM) and next generation firewalls (NGFWs), is required to gain a comprehensive view of potential threats across IT and OT environments.
“Developing a standardized methodology for data collection that is scalable, reliable and secure can enable new use cases without reducing an organization’s security posture,” says Dan Behrens, marketing engineering, IoT, Cisco. Solutions should not require direct device access and should support industrial security standards, such as the use of an industrial demilitarized zone (IDMZ). By deploying and developing an organizational standard approach to data collection, manufacturers can quickly adopt new technologies, and vendors will not have to develop and support one-off solutions for every area/application. Behrens notes two applicable industrial security standards to support and follow are IEC 62443 and NIST 800-82.
Another useful website to keep up with ICS hardware and software is the Department of Homeland Security’s ICS-CERT (Industrial Control Systems Cyber Emergency Response Team site). ICS-CERT provides alerts and advisories, an e-newsletter and reports to keep ICS users up to date on cybersecurity issues and ICS hardware/software updates. It also provides an "Introduction to Recommended Practices" in securing systems from cyber threats, showing control systems vulnerabilities and attack paths, plus defining a secure architecture design.
When looking for tools to monitor and protect ICS networks, Boulting’s Boughton suggests that tools be designed and built on standards such as IEC/ISA-62443. “It provides guidance on policies and procedures surrounding personnel, physical and network security, risk management and implementation, training and awareness, and incident planning and response. It also explores system architecture, network segmentation and individual components, such as PLCs, HMI devices, PC stations and firewalls,” adds Boughton.
“Legacy poll/response PLCs are the most insecure piece of the industrial network,” says Travis Cox, co-director of sales engineering at Inductive Automation. “We feel it is important to protect PLCs, and typically that is done through firewalls. Today, we recommend using edge gateways in front of PLCs. The edge gateway will talk to the PLC directly, so the PLC is not exposed to the entire network. That allows the polling to be at the edge of the network. The data can be published to a MQTT server, securely allowing for a more efficient and secure network.”
MQTT is a critical part of the OT/IT convergence, adds Cox. Used in IIoT applications, MQTT is an open-standard, message-oriented middleware that is bandwidth friendly. With MQTT, data is reported by exception. MQTT allows data to flow to multiple applications, such as SCADA, ERP, etc.
On the industrial monitoring side, Siemens offers security monitoring and industrial anomaly detection solutions that can be seamlessly integrated into SCADA networks, says Stefan Woronka, head of business development, Industrial Security Services, Siemens Digital Factory. Industrial anomaly detection is a 100 percent passive solution that takes all telegrams of SCADA networks by copying them through a TAP or SPAN port and analyzing them. With this system, all participants (endpoints) in the network are identified, a communication matrix created (who’s talking to whom), and finally the basis for monitoring for anomalies is created. Industrial security monitoring adds an active component to detection as the system watches and captures all security events.
Similarly, Cisco’s Industrial Network Director is capable of discovering industrial endpoints by actively communicating to end devices in the protocols they were designed to speak, such as Common Industrial Protocol (CIP), Profinet, Modbus TCP, OPC UA and others, says Cisco’s Behrens. It leverages this information to provide operations teams with visibility into what assets are on the network, where they are located and how the network is performing. This industrial context can also be shared with Cisco’s Identity Services Engine (ISE).
ISE provides a centralized location to define security policies and enforce them dynamically across the infrastructure. In addition, Cisco’s Stealthwatch provides the ability to collect and learn traffic flows across the network and alert on any changes. Should an endpoint start talking to other devices it hasn’t historically communicated with, Stealthwatch can help identify and alert an operator on the new pattern. Behrens also notes that his company provides advanced services that deliver a rich industrial deep packet inspection to uncover what is being communicated between devices and provide alerts on traffic deviations.
Two DMZs at the enterprise level
Security at the enterprise level can use many of the same technologies that bolster the system at the OT level. But, according to defense-in-depth (DiD) principles, which use a layered approach to security, a DMZ should restrict traffic flow between the IT and OT levels and another should be between the IT level and the internet or cloud.
“The same logic applies here: the application of the defense-in-depth concept,” says Siemens’ Woronka. “Multi-layered also means the application of a proper zones conduit model, by which all systems (SCADA systems, MES, ERP) shall be put into zones that are independent from each other.” Siemens accomplishes this level of protection by using Palo Alto Networks next generation firewalls for conduits between these layers. Palo Alto Networks has an OEM partnership with Siemens.
It’s important to follow the best practices, such as IDMZ technologies, to limit appropriate data flows, says Cisco’s Behrens. Segmentation to reduce the scope of access and visibility into traffic flows across the environment can reduce the likelihood of unauthorized data collection and, in return, reduce an organization’s threat surface.
Defining data flows in advance can be an important step to take when emergency communications in the future may depend upon specific connections, unimpeded by cybersecurity breaches. For example, in food and beverage, communications are vital during recalls, says Behrens. “Once we have been made aware of a potential recall situation, one should leverage data for [supply] chain distribution to understand where the affected products are so they can be accurately targeted. There is so much at stake for recalls (safety, timeliness, brand equity and so much more), making it vital that we can identify impacted products that have been shipped so appropriate action can be taken.”
Take it to the cloud
One possibility that may help to ensure the security processors need is to consider cloud-based MES and ERP for the disaster recovery support inherent in automatic backups and the redundancy of the cloud, says Circadence’s Lee. “However, regardless of on-premise or cloud implementation, best practices show that evaluating the risk of MES and ERP software and then monitoring the key terrain, such as the HMIs and supporting data, are critical protection requirements.”
“I think we need to understand that it is not ‘one size fits all’ in terms of a cloud and edge strategy for manufacturing,” says Cisco’s Behrens. Gartner research firm recently stated “the edge will eat the cloud,” and what it meant was (in terms of latency, speed and security) that manufacturing needs to evaluate all of its options and make the right decision on its own, says Behrens. “That said, a combination of edge/hybrid [schemes] to reduce data to the cloud and securely share across multiple organizations seems to be a solid solution.”
Related Articles
When connecting to the cloud, the application of the DiD concept is mandatory, says Siemens’ Woronka. To send data out of a SCADA system, Siemens recommends a perimeter network (or DMZ). This perimeter network hosts all services that will receive data from the outside (e.g., office or cloud), such as Windows updates and antivirus updates. This may be a cloud solution based on MindSphere (the Siemens IIoT operating system) or other services, such as historical data.
Best practices for securing MES/ERP communications are no different than those for OT, according to Boulting’s Boughton. A survey of current equipment and software used in any environment needs to be the first consideration. Validation testing of new software should be performed in an environment external from production. Once validated and placed into operation, new software that connects to the cloud needs to be kept updated to maintain security.
Circadence’s Lee points out a few other key considerations to ensure the safety and security of connecting with cloud-based systems. First, ensure that the most sensitive data is only accessible to certain trusted personnel and that all employees on the IT and OT sides are aware of the risks when using personal devices within the facility. Strong encryption, AI and machine learning solutions can help create responsive threat intelligence, intrusion detection of anomalies and prevention efforts.
Also, processors should conduct live-fire, tabletop exercises (TTX) with IT and OT cyber teams in emulated cyber ranges to help determine effectiveness of cybersecurity protection strategies and ensure they are synced across physical and cloud-based domains. These exercises will help processors to see whether their protection strategies are built into the lifecycle or if patched security add-ons are hindering a stronger security posture. Finally, Lee suggests that limiting access to HMI (e.g., what IP addresses and users can connect) is good practice, as well as monitoring and protecting the company’s data historian.
One nagging issue concerns external logins to the network from supply chain members. Boughton warns that all users should be under control of an administrator (or a team, depending on the size of the business). Tight control of accounts is vital, combined with short password validity (or lack thereof) and automatic deletion if an account goes unused for a period of time.
“We recommend using centralized identity management through trusted federated identity technologies, such as SAML and OpenID Connect,” says Inductive Automation’s Cox. “Identity providers, such as Okta, Duo, ADFS and Ping iD, offer multifactor authentication and SSO. These are standard IT practices. We also need to ensure that within the applications, such as SCADA, that users only get access to their information. That can be done through ACLs (access control lists) from a data and application perspective. It is also incredibly important to turn on auditing in all systems to properly monitor access. Organizations need to have a plan to review the audits on a continuous basis.”
6 predictions for industrial security professionals in 2019
Though industrial control systems (ICSs) have been running critical infrastructure and manufacturing since the 1950s, only in the last few years have they undergone a coming of age with security. This is primarily due to a confluence of events that have propelled OT threats to the C-suite risk agenda.
Based on Indegy experts’ daily interactions with professionals working to secure their ICSs, we have pulled together the following predictions about the 2019 industrial security landscape.
1. ICS security will become more mainstream
Many large industrial and critical infrastructure organizations have already made investments to secure their OT infrastructure to the same or even a higher degree than their IT infrastructure. We expect this trend to continue throughout 2019. In addition, we predict it will extend beyond large organizations to midsize and smaller companies.
2. Hacking tools for critical infrastructure will be more accessible
There is no question that many past attacks have been conducted by nation-states, rogue factions and insiders. Going forward, we will likely see lone wolves and non-nation actors also launching attacks as the barriers to entry are lower, and with a little know-how, OT-based attacks can be carried out by the general hacking community.
3. Attacks will continue to get more sophisticated
Attacks will become multi-pronged, targeting various locations and sites simultaneously or in close succession. Organizations will need to consider this possibility and evolve their security posture accordingly.
4. Active detection will be too valuable to ignore
Active threat hunting through safe device querying will become essential in order to gain the visibility, security and control necessary to protect against a new generation of threats. “Active” covers the 50 percent of threats that can’t be detected with passive, network-only monitoring. Many OT security vendors are only now adding rudimentary active capabilities.
5. More collaboration/sharing of OT threat intelligence
This year, we are likely to see a maturation of ICS threat intelligence. This includes the use of external security data feeds as well as integrating OT security technologies with security information and event management systems (SIEMs), next generation firewalls, etc. There will also be more sharing of information across communities such as the Open Information Security Foundation (OISF), which has been a mainstream practice for years in IT.
6. Real standards for ICS security will emerge
We will see new ICS-specific standards, guidelines and best practices for assessing and hardening the security of ICS environments published and adopted. Looking at 2019 and beyond, ICS threats will continue to escalate and evolve, but we predict the solutions to combat these threats will effectively address whatever emerges.
—Mille Gandelsman, CTO, Indegy
Resources:
“Recommended Practice: Improving Industrial Cybersecurity with Defense-in-Depth Strategies,” ICSCERT, Department of Homeland Security, September 2016
“Hacking 101,” Frank Heidt, TEDX Midwest Talk, Video, YouTube
“State Sanctioned Hacking—The Elephant in the Room,” Frank Heidt at TEDX Midwest Talk, Video, YouTube
“Recommended Practice: Updating Antivirus in an Industrial Control System,” NCCIC, ICS-CERT, Department of Homeland Security, IR-18-214, Aug. 2, 2018
NIST Cybersecurity Framework, NIST Website
ICS-CERT (ICS Cyber Emergency Response Team), https://ics-cert.us-cert.gov/
“Control Systems Cybersecurity: Defense-in-Depth Strategies,” David Kuipers, Mark Fabro, Idaho National Laboratory, May 2006
For more information:
Boulting Technology, www.boultingtechnology.co.uk
Circadence, www.circadence.com
Cisco Systems, www.cisco.com
Claroty, www.claroty.com
CRB, www.crbusa.com
Indegy, www.indegy.com
Inductive Automation, www.inductiveautomation.com
PTC, www.ptc.com
Rockwell Automation, www.rockwellautomation.com
Siemens, www.siemens.com/industrialsecurity
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





