Knowing Vulnerabilities In OT Systems Can Help Cybersecurity Efforts
While a hacker may not gain access directly to a processor’s sensor/actuator digital network, the nefarious individual could gain access to controlling a fermentation system through un-patched controllers or by using remote desktop protocols (RDP) to a supervisory user interface, allowing direct access to the controls such as in the break-in to the Oldsmar, Fla., water treatment facility. Photo credit: Background industrial shot, Wayne Labs; and foreground hacker image, Gerd Altmann from Pixabay.
According to the IBM “X-Force Threat Intelligence Index 2022,” ransomware was the number one attack type in 2021, accounting for 21% of all attacks. Sixty-one percent of incidents at OT-connected organizations last year were in the manufacturing industry. In addition, 36% of attacks on OT-connected organizations were ransomware, according to IBM.1
While a food company like Mondelēz may experience a ransomware IT break-in, extorting money and stealing business/personal data, that doesn’t mean cybercriminals are only going for enterprise-level targets. In fact, OT (operational technology) attacks are also in vogue as demonstrated by the attack of the Oldsmar, Fla. fresh water treatment center. These OT attacks, while seemingly aimed only at high-stakes targets like oil and gas or the electrical grid, could be just as devastating to a food or agri-food company where sensitive ICS equipment is used.
However, OT attacks can be minimized by having an exhaustive picture of facility networks—all the way from device level to OT and to IT networks. Through good engineering practices (secure by design), many attacks on OT systems can be thwarted by using firewalls and routers correctly (and keeping their rules updated), knowing data flows and directions in the entire plant network, minimizing the use of remote desktop protocols (an open invitation to hackers to take over control systems as demonstrated by the Oldsmar break-in) and training operators on human engineering tactics used by cyberattackers. For a processor whose engineering staff thinks an OT device may be directly open to the internet, one way to check is by doing a search on Shodan.io for devices exposed to the public internet.2
CISA and OT:ICEFALL
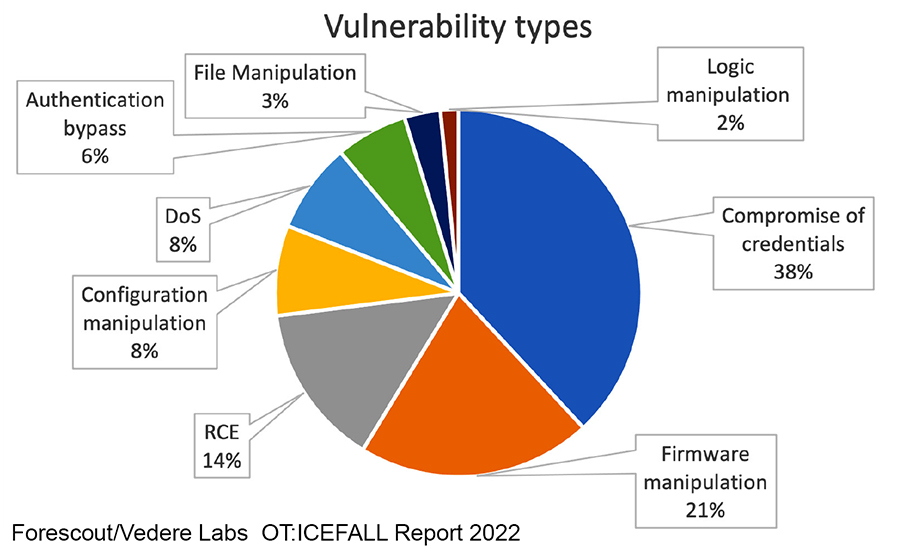
Recently, CISA (the U.S. Cybersecurity & Infrastructure Security Agency) released several advisories related to an “OT:ICEFALL” (Insecure by Design) Report from Forescout’s Vedere Labs.3 Forescout has discovered a set of 56 vulnerabilities affecting 26 devices from ten operational technology (OT) vendors caused by insecure-by-design practices in OT. The affected products are known to be prevalent in several critical industries employing this technology. According to Forescout, many of these products are sold as “secure by design” or have even been certified with OT security standards.

CISA, whose mission is to defend ICS environments, offers a wide range of free products and services to support the ICS community’s cybersecurity security risk management efforts. CISA publishes an up-to-date list of ICS equipment and systems advisories regarding patch statuses and risk assessments.4
According to the Forescout report, OT vulnerabilities are divided into four main categories: insecure engineering protocols, weak cryptography or broken authentication schemes, insecure firmware updates and remote code execution (RCE) via native functionality. Among the vulnerabilities found, 38% allow for compromise of credentials, 21% for firmware manipulation and 14% for remote code execution. The report found 74% of affected product families have some form of security certification.
Cybersecurity is fundamental for the safe operation of industrial control systems, due to an emerging threat landscape with new cybercriminals and targets and the increased connection between IT and OT systems. Today, threats targeting industrial equipment include internal and external attackers, for example, disgruntled employees, hacktivists, cyber criminals, and state-sponsored parties. Threats in the OT space have evolved significantly, showing more disruptive and destructive intent over the last decade.
According to the Forescout report, high-profile malware using OT technologies include Industroyer, which was used to cause Ukraine power outages in 2016, and the newer Industroyer2 variant found in Ukraine in 2022; TRITON, which targeted industrial safety systems in the Middle East in 2017; and INCONTROLLER, an APT toolkit targeting several OT devices, such as OPC UA servers and PLCs from Omron and Schneider Electric, according to the Vedere Labs report.
Secure-by-design vs. insecure-by-design
Today, most all ICS equipment is designed to be secure, meaning that software products and capabilities have been engineered to be foundationally secure. Unfortunately, much older equipment wasn’t designed to be capable of withstanding direct hacks and tampering. Modbus equipment, for example, wasn’t necessarily designed to be cybersecure. But now Modbus-based equipment is among some of the equipment to have common vulnerabilities and exposures (CVEs).

Unfortunately, risk management is complicated by the lack of known CVEs, says the Forescout report. It’s not enough to know that a device or protocol is insecure. To make informed risk management decisions, asset owners need to know how these components are insecure. Issues that considered the result of insecurity by design have not always been assigned CVEs, so they often remain less visible and actionable as they should.
According to the Forescout report, there are insecure-by-design supply chain components, and the vulnerabilities in them tend not to be reported by every affected manufacturer. Vedere researchers looked at two vulnerabilities with CVEs assigned to the ProConOS runtime that is often used in PLCs and RTUs without an associated CVE or public discussion that they were affected.
How should processors look at this situation?
While all these issues are serious, they may not necessarily be impactful if otherwise secure-by-design engineering principles are followed in system development. Ron Fabela, CTO & co-founder at SynSaber5 , a provider of industrial asset and network monitoring solutions and SCADA security systems, explains:
“These CVEs focus on architecture, which stems from requirements for reliability but appear insecure by design. These would require complete refactoring or redesign to address as one cannot simply ‘patch Modbus.’ Past industrial vulnerability disclosures felt very familiar with typical software vulnerabilities that had some hope of being patched, although the dreaded ‘forever-day’ vulnerabilities still do exist, where the vendor refuses to or cannot generate a patch for that system.
“OT:ICEFALL, by design, set out to take these previous insecure-by-design elements and generate CVEs with the expected outcome of bringing more attention to these underlying issues. In reality, these unfixable issues have now exceeded managing and reporting thresholds for critical infrastructure, especially regulated industries like electric utilities. Now that CVEs have been identified, and ICS advisories posted by CISA, asset owners have no choice but to answer the following questions: Are the affected products in my environment? And, if so, what is the plan to patch or remediate?
“This has already kicked off a scramble to answer these questions and, more importantly, keep track of multiple CVEs that can never be actioned,” says Fabela.
“While I understand and appreciate the intent of OT:ICEFALL, the potential impact on the community, as a result, was either not fully understood or dismissed,” Fabela adds. “Researchers looking for high CVE counts and a blog post could now literally generate 100s or 1000s more meaningless disclosures, restating the same issues that asset owners, vendors, and operators can do little about. The ICS security community should be looking for ways to work with product security at OEMs and asset owners to drive real engineering informed security to remove these insecure-by-design flaws. Keeping our critical infrastructure teams buried in busy work CVEs is not the way.”
Resources:
1“X-Force Threat Intelligence Index 2022,” IBM Security, IBM Corporation, Armonk, NY, 2-2022; USA
2“Shodan: Search Engine for the Internet of Everything,” https://www.shodan.io/
3Forescout: “OT:ICEFALL: 56 Vulnerabilities Caused by Insecurity-by-Design Practices in OT;” webinar and research study; accessed 29 June 2022; https://www.forescout.com/research-labs/ot-icefall/
4“CISA Releases Security Advisories Related to OT:ICEFALL (Insecure by Design) Report,” CISA, 28 June 2022, https://www.cisa.gov/uscert/ncas/current-activity/2022/06/22/cisa-releases-security-advisories-related-oticefall-insecure
5SYNSABER Web site, https://synsaber.com/
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!








